AI Powered Cyberattacks : 2025 Master Defense Guide | Secure Your Future
Artificial intelligence thanks to its ability to process huge amounts of data recognize patterns and autonomously learn has transformed a myriad of industries. But the very same capabilities which promise to bring innovation can also pose an extremely risk when used for malicious reasons.
AI powered cyberattacks are distinguished in their rapidity flexibility and sophistication. They are far beyond the capabilities of traditional attacks that are led by humans. Attackers use AI to perform all sorts of things from targeted profiling to more sophisticated malware design and auto-poring.
The dual nature of AI is a potent tool that can be used for defense and offense is creating a distinct battle in the digital space.

Rapid advances of machine learning (ML) as well as deep learning (DL) and the natural process of language (NLP) change the playing field requiring constant adjustments from the defense. It is important to recognize that the opponent isnt static; they continue to refine their AI strategies for attack.
Read Also – From Chatbots to Copilots: The Evolution of AI in Everyday Life 2025
Understanding the AI Powered Threat Landscape in 2025
To be able to defend effectively against attacks powered by AI It is essential to be aware of the many techniques that AI can be used to weaponize. Below is a list of most important threat categories:
- Automated Reconnaissance and Target Profiling:
- Artificial Intelligence-driven gathering can allow attackers to search the web as well as social media and the dark web to find vulnerabilities employees information vulnerabilities as well as networks.
- Analytical predictive analysis for attacks aids in identifying those entry points that are most likely to be successful.
- Social analysis of behavior for engineering allows phishing ads to be tailored specific to the target group which makes the campaigns extremely convincing. This is of great concern to the prevention of social engineering.
- Advanced Phishing and Spear-Phishing Campaigns:
- AI generated phishing messages can be easily distinguished from legitimate ones with flawless grammar and understanding.
- Video and voice fraud are now a major threat that allow hackers to appear as people who are trusted or executives using alarming realism. This is why the detection of fakes an essential ability.
- Contextual Phishing adjusts the content it offers to the users internet activity and their interests. increasing the probability of success.
- Polymorphic and Evasive Malware:
- Artificial Intelligence-powered malware will constantly alter its code to avoid the signature-based systems for detection.
- Automated malware development utilizes AI to develop new malware which reduce the requirement to rely on human intervention.
- Malware that is stealthy will learn to adapt network behaviours that allow it to stay undetectable and dormant for long periods of time which allows persistence in security issues.
- Automated Exploitation and Vulnerability Discovery:
- AI to prevent zero-day exploitation will quickly scan the code of software for weaknesses which havent yet been identified by the manufacturers.
- automated penetration test instruments driven by AI are able to autonomously detect and exploit weak points in both networks and systems.
- Adversarial AI that can bypass security controls discovers ways to fool defense systems based on AI to misclassify criminal activity as legitimate. This is the most fundamental component of adversarial machine learning.
- Distributed DDoS (DDoS) Attacks using AI Orchestration
- Botnets that are intelligent make use of AI to coordinate complicated DDoS attacks and adapt attacks patterns so that they can bypass attempts to mitigate.
- DDoS attacks that are adaptive are able to be taught from defensive actions and alter their strategy as they go along making defense strategies against DDoS harder.
- Supply Chain Attacks and Software Vulnerabilities:
- AI driven supply chain exploit detects vulnerabilities in software and parts from third parties that allow attackers to attack the security of an enterprise through trusted suppliers.
- Automatic software vulnerability scanning is a weapon that can detect flaws in commonly used programs.
- Data Exfiltration and Insider Threats:
- Artificial Intelligence-powered data theft can identify and protect important data decrypt it then transfer the data secretly.
- In-depth threat identification using AI could be defeated using AI powered tactics that replicate normal user behaviour to avoid the suspicion of a user which is a distinct issue to the prevention of data loss (DLP).
The Pillars of Defense: Building Resilience Against AI Powered Cyberattacks
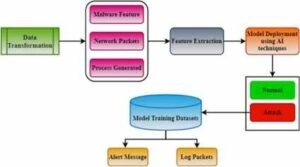
To defend from attacks powered by AI requires a multi-layered active and flexible method. The conventional security strategies arent enough for organizations to adopt an AI first cyber security strategy. These are the most important foundations of the strategy:
Enhancing Your Perimeter Security by enhancing security with AI
The initial step is to use AI to recognize and deter dangers at the edges of networks.
- Next-Generation Firewalls (NGFW) equipped with AI: Implement NGFWs which use AI to detect anomalies and identifying patterns of unusual traffic and blocking sophisticated hacks that override signature-based rules. They are essential to the network security options.
- Intrusion detection and prevention systems (IDPS) driven by Machine Learning: Advanced IDPS platforms employ machine learning in order to analyse patterns in the network find indications of compromise (IoCs) and then prevent malicious activities. This helps improve the threat intelligence capabilities of platforms.
- AI driven Email Security Gateways They employ AI to study email contents reputation of the sender as well as behavioral clues to recognize and eliminate sophisticated spear-phishing and phishing as well as Business Email Compromise (BEC) threats. This is crucial to email security good methods.
- Web Application Firewalls (WAF) equipped with Behavioral Analytics AI enhanced WAFs are able to learn typical behavior in applications making them extremely effective in blocking advanced cyber attacks like SQL injection as well as cross-site scripting (XSS). This translates into solid app security.
Advanced Endpoint Detection and Response (EDR) that incorporates AI
Endpoints (laptops desktops servers mobile devices) are frequent targets. AI powered EDR is crucial to protect the endpoints.
- AI enabled Endpoint Security Platforms (EPP): These options go beyond conventional antivirus utilizing machine-learning to recognize fileless malware polymorphic threat types as well as zero-day attacks. They also provide sophisticated threat protection.
- Behavior analytics for endpoint security EDR systems use AI to observe the behavior of users and the endpoints. They can identify any deviations which may indicate compromise and even emerge from new attacks. This aids in the analysis of user behavior (UBA).
- Automated Incident Resolution on Endpoints AI will automate remediation steps like blocking compromised devices destroying malware-generating processes or the rolling back of system changes and reducing dwell time. It is the foundation of automated incident response.
- Threat Hunting using AI Assistance AI is able to analyse huge quantities of data from endpoints to find subtle indications of compromise that humans may miss thus enhancing the effectiveness of threat hunting..
Identification and Access Management (IAM) using AI Integration
Credentials that are compromised are the main source of security breach. AI strengthens IAM.
- AI powered Multifactor Authentication (MFA): Adaptive MFA systems make use of AI to determine risks (location the device or location and the time of day) prior to prompting additional authentication. This makes it difficult for attackers to evade. This is crucial to security of identity.
- Behavioral Biometrics AI can identify unique patterns of user behavior (typing patterns or mouse motions) to authenticate users continuously without input from the user offering an effortless and safe service. This increases security by using biometric security.
- Privilege access Management (PAM) that uses AI Artificial Intelligence helps detect and identify suspicious activities around privilege accounts. These are ideal targets for hackers because of their higher access rights. This is essential to secure privileged account security.
- Access Review and anomalous Detection: AI can help automate reviewing users access rights and also identify abnormal access patterns. This can help in enforcing the principle of the least privilege. This can help strengthen access control guidelines.
Security Information and Event Management (SIEM) and Security Orchestration Automation and Response (SOAR) that incorporates AI
The consolidation and use of security information is crucial. AI boosts SIEM and SOAR.

- AI driven SIEM solutions: Contemporary SIEM solutions make use of AI to connect security incidents across the whole IT infrastructure detect complex attacks and then make alerts more priority thus reducing alarm fatigue among analysts. This helps improve the efficiency of log management and analyze.
- user and entity behavior Analytics (UEBA): UEBA is a key component of AI driven SIEM it tracks normal behaviors of entities and users so it is highly efficient in finding insider threats as well as compromised accounts. It is vital to detectable anomalies.
- SOAR Platforms that incorporate AI for automated response AI infused SOAR platforms can automate the complex workflows for incident response by taking steps like blocking IP addresses quarantining files and enhancing alerts with threat intelligence. This dramatically speeds the response time. This improves security operations centre (SOC) effectiveness.
- Predictive Security Analytics AI analyzes past attack information and threat information to anticipate attack scenarios which allows companies to strengthen their defenses in advance. This helps with the risk management.
data Security as well as Cloud Security with AI
The protection of sensitive information as well as cloud systems against AI powered attacks requires special methods.
- AI powered AI powered Loss Prevention (DLP): advanced DLP tools make use of machine learning in order to precisely sort sensitive data keep track of the movement of data and stop unauthorised data loss including advanced AI powered attempts. It also ensures the privacy of data.
- Cloud Security Posture Management (CSPM) that incorporates AI: AI driven CSPM tools continually check cloud configurations for errors and weaknesses that could be exploited by attackers using AI. This is essential to cloud security best methods.
- Cloud Workload Prevention Platforms (CWPP) equipped with behavioral AI: CWPPs use AI to guard cloud-based workloads (VMs containers servers functions) by defining normal behaviour and identifying anomalous behavior. This improves the containers security.
- Key Management and Encryption: While not directly powered by AI strong encryption techniques provide the foundation for security of data. security which renders data that has been accessed not useful to attackers. The best encryption practices cannot be negotiated.
Human Factor and Continuous Training
Even in the midst of modern AI protections the human component remains an important threat and an essential defense.
- Secure Awareness Training (SAT) with AI Intelligence: Use AI to identify common attack patterns and customize security awareness programs that target specific weaknesses within the workforce. It is crucial to humans to develop their firewalls.
- Simulated Phishing as well as Social Engineering Tests: Every week conduct AI powered simulated hacking and social engineering threats to measure the resilience of your employees and determine areas that require additional education. This assists with security assessment of posture.
- Cybersecurity Skills Development Make sure you train your security team on the use of AI in cybersecurity machine learning security and artificial intelligence adversarial strategies to recognize and mitigate advanced security threat. This will ensure the security of your workforce.
- Incident Response Training Do regular drills as well as tabletop activities to help prepare your teams incident response to handle AI powered hacks that emphasize the speed of response and coordination. This helps build strong security teams.
Proactive Threat Intelligence and Research
Being ahead of the game is a constant process of learning and collecting.
- AI driven threat intelligence platforms Make use of platforms that employ AI to collect analyse and share live threat information which includes details on the latest AI powered techniques for attack. This is vital to cybersecurity security..
- Participation for Industry Collaboration Connect with industry organizations Information-sharing organisations (ISACs/ISAOs) and cybersecurity groups to exchange information and the best practices in dealing with AI threat vectors. This helps to strengthen protection of the community.
- The investment in Research and Development: Companies should make investments in and partner with companies studying AI security as well as defense AI in order to create the most cutting-edge security measures. This will drive technological innovation in cybersecurity..
- patching and Vulnerability Management Although fundamental having an effective vulnerability management software is vital. AI helps in the selection of patches according to exploitability as well as impact.
The Future of Cyber Defense: Embracing Defensive AI
The fight against cyberattacks that are powered by AI is likely to be increasingly battled with AI. The idea behind defense AI includes using AI to identify analyse and eliminate AI driven threats. This is a part of:
- Automatic Security Agents AI powered security agents that are able to be independent and operate to monitor systems spot anomalies and immediately take action to stop them without the intervention of humans.
- Predictive Threat Models AI which can analyse huge amounts of information to identify attack vectors and enhance defenses prior to when any attack occurs.
- Adversarial Machine Learning Defenses: Techniques that train defense AI models to detect and deter attempts from malicious AI to alter their models.
- AI in Automated Malware Analysis Analyzing and rapidly dissecting the behaviour of new malware types.
- threat emulation Red teaming and Threat Simulation utilizing AI: Using AI to create sophisticated attacks on your system to detect weak points.
A Continuous Journey of Adaptation and Innovation
The world of cyberattacks powered by AI in 2025 will be dynamic demanding gruelling and fierce. Companies that do not adapt and integrate AI as part of their defense tactics will be being disadvantaged. The secret to resiliency lies in the holistic approach which integrates AI throughout all aspects of security – from the point of entry to cloud detection through to.
The master guide provides an extensive framework. However its important to understand that cybersecurity isnt an endpoint but a constant adventure of adapting learning and new ideas. Making investments in the best tools building a robust security environment constantly informing your staff as well as staying up-to-date with new threat information are essential. Through harnessing the potential of AI to defend ourselves and a defender we could shift the balance towards our benefit securing the privacy of our data assets as well as our future against this ever-changing danger. Our future in cyber security will depend on our capacity to beat attackers equipped with automation intelligence as well as the powerful ability of defense AI.
